free software
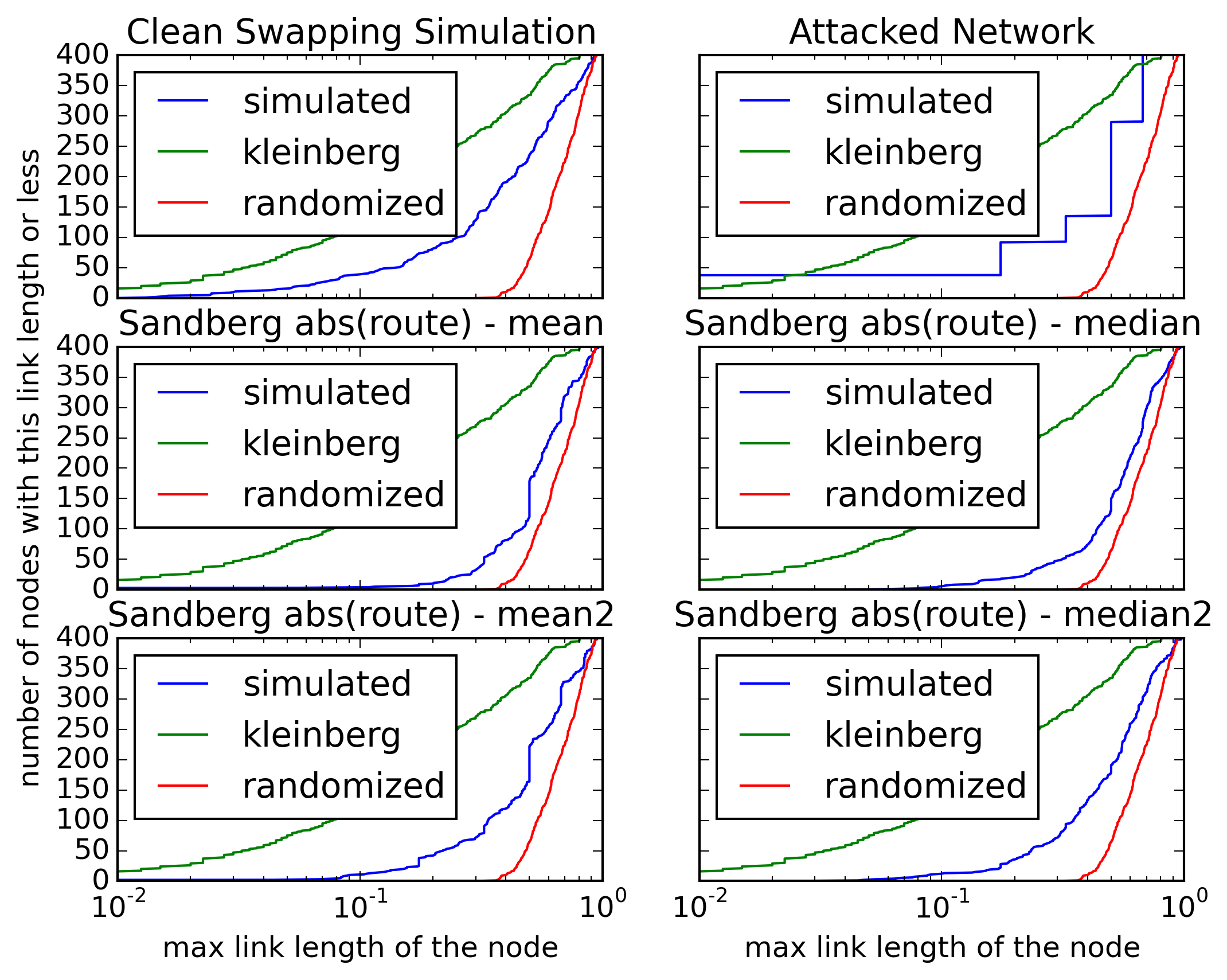
Mitigate the Pitch Black attack (the simulation works)
Mo, 02/08/2016 - 11:37 — DraketoI fixed a small bug in the simulator of thesnark. With that, the simulator shows that the defense against the Pitch Black Attack works: A small number of attackers can no longer kill parts of the keyspace and can also no longer make certain parts of the keyspace inaccessible.
Attackers can still limit the convergence of the network towards a reproduction of the small world network, but since we know that Opennet works quite well with 30% backoff, this limited convergence should suffice for efficient routing.
- Login to post comments
- Weiterlesen
Python chooses Github, therefore I’m releasing the py2guile PDF for free
Mi, 01/06/2016 - 23:54 — DraketoPython is the first language I loved. I dreamt in Python, I planned in Python, I thought I would never need anything else.
Download “Python to Guile” (pdf)
You can read more about this on the Mercurial mailing list.
- Free: html | pdf
preview edition
(complete)
Yes, this means that with Guile I will contribute to a language developed via Git, but it won’t be using a proprietary platform.
- Login to post comments
- Weiterlesen
Translating a lookup-dictionary to bash: Much simpler than I thought
Mi, 10/21/2015 - 18:18 — DraketoI wanted to name Transcom Regions in my plots by passing their names to the command-line tool, but I only had their region-number and a lookup dictionary in Python. To avoid tampering with the tool, I needed to translate the dictionary to a bash function, and thanks to the case statement it was much simpler than I had expected.
This is the original dictionary:
- Login to post comments
- Weiterlesen
GNU Guix in 5 minutes
Mo, 10/19/2015 - 16:48 — DraketoSo you get excited when you hear about surviving a power-outage during updates without a hitch and you want to give Guix a try — but woes, you only have 5 minutes of time?
Fear not, that’s enough to get it up and running — all the way to per-user environments and package install as non-priviledged user!
The instructions here are from the official docs, specialized for a GNU Linux host and cut to what I need in a working system.
as user:
$ cd /tmp
$ wget ftp://alpha.gnu.org/gnu/guix/guix-binary-0.8.3.x86_64-linux.tar.xz
- Login to post comments
- Weiterlesen
Gratis py2guile from Freenet
Sa, 10/17/2015 - 12:04 — Draketopy2guile is a book I wrote about Python and Guile Scheme. It’s selling at 14.95 € for the printed softcover.
To fight the new german data retention laws, you can get the ebook gratis: Just install Freenet, then the following links work:
Escape total surveillance and get an ebook about the official GNU extension language for free today!
- Login to post comments
BY-SA and GPL: creativecommons closed the chasm in the sharealike/copyleft community
Do, 10/08/2015 - 18:03 — DraketoThis is the biggest news item for free culture and free software in the past 5 years: The creativecommons attribution sharealike license is now one-way compatible to the GPL — see the message from creativecommons and from the Free Software Foundation.
- Blender rigs under cc by-sa which use libraries under GPL are safe against suing, even if a Blender code contributor goes crazy,
- 3D models like the self replicating 3D printer RepRap and libre hardware designs under cc by-sa and GPL can be combined,
- GPL-compatible Free Software can utilize all content from the Wikipedia and
- On the personal side: we can merge art from Ryzom and Battle for Wesnoth and use both in the Pirate Party RPG.
Some license compatibility legalese might sound small, but the impact of this is hard to overestimate.
- Login to post comments
- Weiterlesen
Going from Python to Guile Scheme - a natural progression
Do, 10/01/2015 - 21:42 — DraketoPython is the first language I loved. I dreamt in Python, I planned in Python, I thought I would never need anything else.
- Free: html | pdf
- Softcover: 14.95 €
with pdf, epub, mobi
- Source: download
free licensed under GPL
- Login to post comments
- Weiterlesen
Using Guile Scheme Wisp for low ceremony embedded languages
Sa, 09/12/2015 - 22:39 — DraketoUpdate 2020: In Dryads Wake I am starting a game using the way presented here to write dialogue-focused games with minimal ceremony. Demo: https://dryads-wake.1w6.org
Update 2018: Bitbucket is dead to me. You can find the source at https://hg.sr.ht/~arnebab/ews
Update 2017: A matured version of the work shown here was presented at FOSDEM 2017 as Natural script writing with Guile. There is also a video of the presentation (held by Chris Allan Webber; more info…). Happy Hacking!
Programming languages allow expressing ideas in non-ambiguous ways. Let’s do a play.
say Yes, I do!
Yes, I do!
- Login to post comments
- Weiterlesen
Staying sane with Emacs (when facing drudge work)
Mo, 01/26/2015 - 10:04 — DraketoI have to sift through 6 really boring config files. To stay sane, I call in Emacs for support.
My task looks like this:
(click for full size)
- Login to post comments
- Weiterlesen
GnuPG/PGP signature, short explanation
Di, 01/20/2015 - 18:41 — Draketo»What is the .asc file?« This explanation is intended to be copied as-is into emails when someone asks about your signature.
The .asc file is a signature which can be used to verify that the email was really sent by me and wasn’t tampered with.[1] It can be verified with standard email security tools like Enigmail[2], Gpg4win[3] or MacGPG[4] - and others tools supporting OpenPGP[5].
- Login to post comments
- Weiterlesen
Conveniently convert CamelCase to words_with_underscores using a small emacs hack
Mi, 01/14/2015 - 13:07 — DraketoI currently cope with refactoring in an upstream project to which I maintain some changes which upstream does not merge. One nasty part is that the project converted from CamelCase for function names to words_with_underscores. And that created lots of merge errors.
Today I finally decided to speed up my work.
The first thing I needed was a function to convert a string in CamelCase to words_with_underscores.
- Login to post comments
- Weiterlesen
Infinite Hands (Remastered Version)
Do, 12/18/2014 - 16:42 — DraketoMerlin remastered Infinite Hands with Bodhran and Flute. This is a copy of his text (in German).
- Login to post comments
- Weiterlesen
Memory requirement of Python datastructures: numpy array, list of floats and inner array
Di, 12/16/2014 - 16:42 — DraketoEasily answering the question: “How much space does this need?”
Table of Contents
- Login to post comments
- Weiterlesen
Using Macros to avoid tedious tasks (screencast)
Mi, 11/19/2014 - 15:17 — DraketoBecause I am lazy,1 and that makes me fast.
Table of Contents
Screencast
Using Macros to avoid tedious tasks
-
I have lots of stuff to do, so I cannot afford not being lazy ☺ ↩
- Login to post comments
- Weiterlesen
don’t change your habits - fix your tools!
Sa, 10/25/2014 - 08:50 — Draketo→ In don't run 'strings' on untrusted files Michal Zalewski complained that running the strings-utility for computer forensics or other fields of information security could make you vulnerable yourself, so you should not use that. Given that strings is Free Software, I find a different conclusion from the vulnerability of tools used by professional forensics people.
I’d say if you’re actually using these tools to earn money, it is high time to go in and fix them.
- Login to post comments
- Weiterlesen
Free Software
Fr, 09/05/2014 - 09:32 — Draketo„Free, Reliable, Ethical and Efficient“
„Frei, Robust, Ethisch und Innovativ”
„Libre, Inagotable, Bravo, Racional y Encantado“
Articles connected to Free Software (mostly as defined by the GNU Project).
- Login to post comments
- Weiterlesen
A bitcoin-marketplace using Freenet?
Di, 09/02/2014 - 17:53 — DraketoA few days ago, xor, the developer of the Web of Trust in Freenet got in contact with the brain behind the planned Web of Trust for Openbazaar, and toad, the former maintainer of Freenet questioned whether we would actually want a marketplace using Freenet.
I took a a few days to ponder the question, and I think a marketplace using Freenet would be a good idea - for Freenet as well as for society.
Freenet is likely the most secure way for implementing a digital market, which means it can work safely for small sums, but not for large ones - except if you can launder huge amounts of digital money. As such it is liberating for small people, but not for syndicates. For example a drug cartel needs to be able to turn lots of money into clean cash to pay henchmen abroads. Since you can watch bitcoin more easily than cash and an anonymous network makes it much harder to use scare-tactics against competing sellers, moving the marketplace from the street to the internet weakens syndicates and other organized crime by removing part of their options for creating a monopoly by force.
If a bitcoin marketplace with some privacy for small-scale users should become a bigger problem than the benefit it brings by weakening organized crime, any state or other big player can easily force the majority of users to reveal their identities by using the inherent tracability of bitcoin transactions.
- Login to post comments
- Weiterlesen
Download one page from a website with all its prerequisites
Mi, 07/30/2014 - 06:33 — DraketoOften I want to simply backup a single page from a website. Until now I always had half-working solutions, but today I found one solution using wget which works really well, and I decided to document it here. That way I won’t have to search it again, and you, dear readers, can benefit from it, too ☺
Update 2020: You can also use the copyweb-script from pyFreenet:
copyweb -d TARGET_FOLDER URL
Install viapip3 install --user pyFreenet3.
In short: This is the command:
wget --no-parent --timestamping --convert-links --page-requisites --no-directories --no-host-directories --span-hosts --adjust-extension --no-check-certificate -e robots=off -U 'Mozilla/5.0 (X11; U; Linux i686; en-US; rv:1.8.1.6) Gecko/20070802 SeaMonkey/1.1.4' [URL]
Optionally add --directory-prefix=[target-folder-name]
(see the meaning of the options and getting wget for some explanation)
- Login to post comments
- Weiterlesen
Exact Math to the rescue - with Guile Scheme
Mo, 07/21/2014 - 16:48 — Draketo
I needed to calculate the probability that for every freenet user there are at least 70 others in a distance of at most 0.01. That needs binomial coefficients with n and k on the order of 4000. My old Python script failed me with an OverflowError: integer division result too large for a float. So I turned to Guile Scheme and exact math.
Table of Contents
- Login to post comments
- Weiterlesen
USK and Date-Hints: Finding the newest version of a site in Freenet's immutable datastore
Do, 07/10/2014 - 19:47 — Draketo Freenet provides a global, anonymous datastore where you can upload sites which then work like normal websites. But different from websites, they have a version-number.
Freenet provides a global, anonymous datastore where you can upload sites which then work like normal websites. But different from websites, they have a version-number.
The reason for this is, that you can only upload to a given key once1. This data then gets stored in the network and is effectively immutable (much like immutable data structures in functional programming).
-
If you try to upload to a given key twice, you can get collisions. In that case, it isn’t clear which data a client will retrieve - similar to race conditions in threaded programs. That’s why we do not write to the same key twice in practice (though there is a key-type which can be used for passwords or simple file-names. It is called KSK and was the first key-type freenet provided. That led to wars on overwriting files like gpl.txt - similar to the edit-wars we nowadays get on Wikipedia, but with real anonymity thrown in ☺). ↩
- Login to post comments
- Weiterlesen
De-Orchestrating Freenet with the QUEEN program
So, 06/22/2014 - 20:19 — DraketoSo Poul-Henning Kamp thought this just a thought experiment …
In Fosdem2014 Poul-Henning Kamp talked about a hypothetical “Project ORCHESTRA” by the NSA with the goal of disrupting internet security: Information, Slides, Video (with some gems not in the slides).
One of the ideas he mentioned was the QUEEN program: Psy-Ops for Nerds.
I’ve been a contributor to the Freenet Project for several years. And in that time, I experienced quite a few of these hypothetical tactics first-hand.
- Login to post comments
- Weiterlesen
“If you like what I do, why don’t you help me?”
So, 06/22/2014 - 14:23 — DraketoAlmost every free software developer made the experience that many people like his or her work, but very few actually provide help. If you experience this, don’t let it disheart you. Verbal support without practical help sounds inconsistent at first, but it actually is the result of limited time.
Most people who have the skills to help are already committed to other projects, so they cannot help you on yours. They can encourage you from the sidelines (“This is cool!
- Login to post comments
- Weiterlesen
shell basics (bash)
Mi, 05/28/2014 - 13:05 — DraketoThese are the notes to a short tutorial I gave to my working group as part of our groundwork group meetings. Some parts here require GNU Bash.
1 Outline
1.1 Outline
- user-output: echo
- pipes: |, xargs, - (often stdin)
- text-processing: cat/tac, sed, grep, cut, head/tail
- variables (foo=1; echo ${foo})
- subshell: $(command)
- loops (for; do; done) (while; do; done)
- conditionals (if; then; fi)
- scripts: shebang
- return values: $?
- script-arguments: $1, $#, $@ and getopt
- command chaining: ;, &, && and ||
- functions and function-arguments
- math: $((1+2))
- help: man and info
- Login to post comments
- Weiterlesen
The assisted brain and the chained brain
Mi, 05/14/2014 - 20:09 — DraketoWho serves whom? Our tools can be our allies or our masters. Do your tools assist or chain?
- Login to post comments
- Weiterlesen
Schick mir eine verschlüsselte E-Mail
Mo, 04/21/2014 - 17:49 — DraketoEine verschlüsselte E-Mail zu schicken ist einfach. Hier will ich dir in 3 Schritten zeigen, wie du mich erreichen kannst. Ich zeige die Schritte für eine Reihe verschiedener Programme, sowohl für Windows als auch für OSX und GNU/Linux.
Das Programm dafür ist GnuPG: Frei lizensiert und der langjährige Standard für sichere Verschlüsselung von E-Mails.
- Login to post comments
- Weiterlesen
Org-mode with Parallel Babel
Do, 04/03/2014 - 19:42 — DraketoUpdate 2017: a block with
sem -j ...seems to block in recent versions of Emacs until all subtasks are done. It would be great if someone could figure out why (though it likely is the right thing to do). To circumvent that, you can daemonize the job in sem, but that might have unwanted side-effects:sem "[job] &"
Table of Contents
Babel in Org
Emacs Org-mode provides the wonderful babel-capability: Including code-blocks in any language directly in org-mode documents in plain text.
In default usage, running such code freezes my emacs until the code is finished, though.
Up to a few weeks ago, I solved this with a custom function, which spawns a new emacs as script runner for the specific code:
; Execute babel source blocks asynchronously by just opening a new emacs. (defun bab/org-babel-execute-src-block-new-emacs () "Execute the current source block in a separate emacs, so we do not block the current emacs." (interactive) (let ((line (line-number-at-pos)) (file (buffer-file-name))) (async-shell-command (concat "TERM=vt200 emacs -nw --find-file " file " --eval '(goto-line " (number-to-string line) ")' --eval " "'(let ((org-confirm-babel-evaluate nil))(org-babel-execute-src-block t))' " "--eval '(kill-emacs 0)'"))))
and its companion for exporting to beamer-latex presentation pdf:
; Export as pdf asynchronously by just opening a new emacs. (defun bab/org-beamer-export-new-emacs () "Export the current file in a separate emacs, so we do not block the current emacs." (interactive) (let ((line (line-number-at-pos)) (file (buffer-file-name))) (async-shell-command (concat "TERM=vt200 emacs -nw --find-file " file " --eval '(goto-line " (number-to-string line) ")' --eval " "'(let ((org-confirm-babel-evaluate nil))(org-beamer-export-to-pdf))' " "--eval '(kill-emacs 0)'"))))
But for shell-scripts there’s a much simpler alternative:
- Login to post comments
- Weiterlesen
Recursion wins!
Mi, 03/05/2014 - 21:36 — DraketoI recently read the little schemer and that got me thinking about recursion and loops.
After starting my programming life with Python, I normally use for-loops to solve problems. But actually they are an inferior mechanism when compared to recursion, if (and only if) the language provides proper syntactic support for that. Since that claim pretty much damns Python on a theoretical level (even though it is still a very good tool in practice and I still love it!), I want to share a simplified version of the code which made me realize this.
- Login to post comments
- Weiterlesen
Unicode char \u8:χ not set up for use with LaTeX: Solution (made easy with Emacs)
Mi, 01/08/2014 - 11:44 — DraketoFor years I regularly stumbled over LaTeX-Errors in the form of
Unicode char \u8:χ not set up for use with LaTeX. I always took the chickens path and replaced the unicode characters with the tex-escapes in the file. That was easy, but it made my files needlessly unreadable. Today I decided to FIX the problem once and for all. And it worked. Easily.
Firstoff: The problem I’m facing is that my keyboard layout makes it effortless for me to input characters like ℂ Σ and χ. But LaTeX cannot cope with them out-of-the-box.
- Login to post comments
- Weiterlesen
How to fix a bug, using the example of Quod Libet empty panes on Gentoo GNU/Linux (bug solving process)
Mi, 12/11/2013 - 21:29 — DraketoPDF-version (for printing)
orgmode-version (for editing)
For a few days now my Quod Libet has been broken, showing only empty space instead of information panes.
I investigated halfheartedly, but did not find the cause with quick googling. Today I decided to change that. I document my path here, because I did not yet write about how I actually tackle problems like these - and I think I would have profited from having a writeup like this when I started, instead of having to learn it by trial-and-error.
Update: Quodlibet 2.6.3 is now in the Gentoo portage tree - using my ebuild. The update works seamlessly. So to get your Quodlibet 2.5 running again, just call
emerge =media-sound/quodlibet-2.6.3 =media-plugins/quodlibet-plugins-2.6.3. Happy Hacking!Update: I got a second reply in the bug tracker which solved the plugins problem: I had user-plugins which require Quod Libet 3. Solution:
mv ~/.quodlibet/plugins ~/.quodlibet/plugins.for-ql3. Quod Libet works completely again.Solution for the impatient: Update to Quod Libet 2.5.1. In Gentoo that’s easy.
- Login to post comments
- Weiterlesen
Top 5 systemd troubles - a strategic view for distros
Mi, 11/20/2013 - 18:42 — Draketosystemd is a new way to start a Linux-system with the expressed goal of rethinking all of init. These are my top 5 gripes with it. (»skip the updates«)
Update (2019): I now use GNU Guix with shepherd. That’s one more better option than systemd. In that it joins OpenRC and many others.
Update (2016-09-28): Systemd is an exploit kit just waiting to be activated. And once it is active, only those who wrote it will be able to defuse it — and check whether it is defused. And it is starting: How to crash systemd in one tweet? Alternatives? Use OpenRC for system services. That’s simple and fast and full-featured with minimal fuss. Use runit for process supervision of user-services and system-services alike.
Update (2014-12-11): One more deconstruction of the strategies around systemd: systemd: Assumptions, Bullying, Consent. It shows that the attitude which forms the root of the dangers of systemd is even visible in its very source code.
Update (2014-11-19): The Debian General Resolution resulted in “We do not need a general resolution to decide systemd”. The vote page provides detailed results and statistics. Ian Jackson resigned from the Technical Committee: “And, speaking personally, I am exhausted.”
Update (2014-10-16): There is now a vote on a General Resolution in Debian for preserving the ability to switch init systems. It is linked under “Are there better solutions […]?” on the site Shall we fork Debian™? :^|.
Update (2014-10-07): Lennart hetzt (german) describes the rhetoric tricks used by Lennart Poettering to make people forget that he is a major part of the communication problems we’re facing at times - and to hide valid technical, practical, pragmatical, political und strategical criticism of Systemd.
Update (2014-09-24): boycott systemd calls for action with 12 reasons against systemd: “We do recognize the need for a new init system in the 21st century, but systemd is not it.”
Update (2014-04-03): And now we have Julian Assange warning about NSA control over Debian, Theodore Ts’o, maintainer of ext4, complaining about incomprehensible systemd, and Linus Torvalds (you know him, right?) rant against disrupting behavior from systemd developers, going as far as refusing to merge anything from the developers in question into Linux. Should I say “I said so”? Maybe not. After all, I came pretty late. Others saw this trend 2 years before I even knew about systemd. Can we really assume that there won’t be intentional disruption? Maybe I should look for solutions. It could be a good idea to start having community-paid developers.
Update (2014-02-18): An email to the mailing list of the technical committee of debian summarized the strategic implications of systemd-adoption for Debian and RedHat. It was called conspiracy theory right away, but the gains for RedHat are obvious: RedHat would be dumb not to try this. And only a fool trusts a company. Even the best company has to put money before ethics.
Update (2013-11-20): Further reading shows that people have been giving arguments from my list since 2011, and they got answers in the range of “anything short of systemd is dumb”, “this cannot work” (while OpenRC clearly shows that it works well), requests for implementation details without justification and insults and further insults; but the arguments stayed valid for the last 2 years. That does not look like systemd has a friendly community - or is healthy for distributions adopting it. Also an OpenRC developer wrote the best rebuttal of systemd propaganda I read so far: “Alternativlos”: Systemd propaganda (note, though, that I am biased against systemd due to problems I had in the past with udev kernel-dependencies)
- Login to post comments
- Weiterlesen



